Redmine Roles and Permissions – All You Need to Know
Redmine includes a roles and permissions feature that restricts and allows authorized users to access various activities. The tool authorizes team leaders to assign roles and permissions for each project.
Because of this feature, companies protect critical information and limit access roles. Let’s take a look at how roles and permissions help businesses and understand how it is done.
Benefits of Roles and Permissions
Defining roles and permissions is one way that businesses can reduce the risk of cybercrime and data theft. This feature plays a significant role in the security arena as well as enhancing employees' focus by limiting their access to important data. When it comes to security, organizations can integrate role-based access control and restrict network access. Some features of roles and permissions with Redmine include:
Review Roles
Companies are under numerous security threats, especially when they have critical data in their centralized project management tool such as Redmine. Otherwise, cybercriminals can access the tool and disrupt business operations. Therefore, companies set roles and permissions and offer access to limited and trusted users. Managers choose roles and permissions for each of their subordinates.
Redmine enables business managers to authenticate roles based on tasks and projects. When companies bring new users onboard, their team managers create their accounts on Redmine and grant permissions to access projects. This is an essential parameter to secure project management tools from internal and external threats.
Know the Defaults
Role management is a difficult task, but with the right tools and integration, managers can authorize roles and permissions. It is essential to have default settings because mistakes in role authorization result in vulnerabilities. Therefore, many business owners trust Redmine because of its robust security features. This tool makes it easier for supervisors to create and assign accounts and roles.
Access Elevated Permissions
Managers should analyze certain roles before allowing access to their employees. Therefore, they need to create a list with permissions and reduce the risks of vulnerabilities. Redmine is an ideal project management tool when it comes to roles and permissions. These features are simple to use and minimize risks. Furthermore, you can add and remove users from a project using drag and drop features. Isn’t that simple? Here are some sets of permissions or capabilities businesses can assign to their users. These are default permissions, and admins can customize them according to their needs. Let’s take a look:
- Admin
- Author
- Editor
- Subscriber
- Contributor
- Super admin
How to Create Roles and Permissions on Redmine?
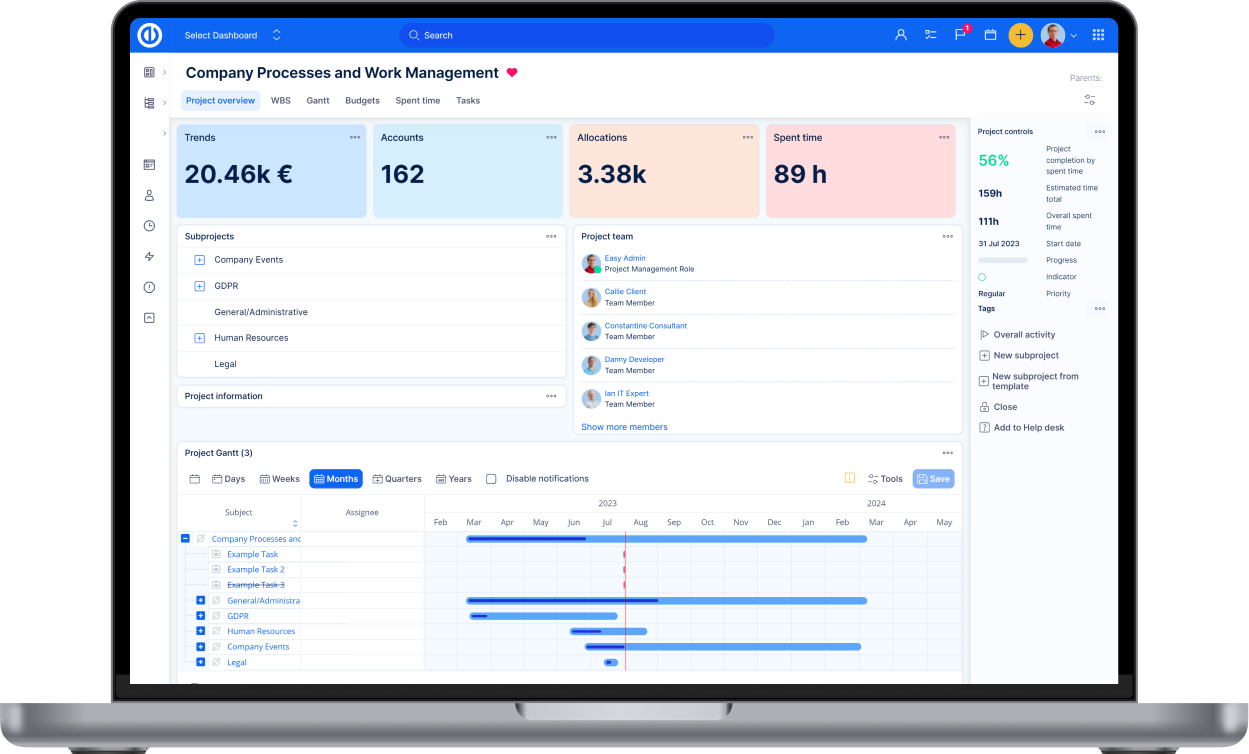
Roles and permissions are easy to configure in Redmine. On the dashboard, you can click on ‘More,’ select ‘Administration,’ and choose the roles and permissions tab. When you click on this option, a page will appear that includes permission reports and existing roles. You can edit names and modify their roles with simple clicks.
Role Properties
When an admin opens the roles and permission page, they can see the following properties:
- Users’ names would be the first option
- Then, the manager will see a checkbox that says assigned roles include issues. If unchecked, the user won’t receive any issue
- Issue visibility allows or restricts the user from viewing issues. Managers can also select from options such as all issues, privacy issues, or issues created by the same user.
An admin can also delete and modify the roles. Also, they can assign other users to edit any role. Redmine offers two default roles that are non-member and anonymous. Redmine use these roles for an internal purpose; thus no one can delete these.
Practices for Roles and Permissions
Managers should understand the importance of assigning roles and permissions. They should restrict and give permissions to different team members after careful evaluation. They should understand what roles each employee performs while choosing an authorized person. An authorized person is an employee who efficiently manages a project. Setting roles and permissions requires certain practices as follows:
1. Ensure Level of Access to Each User
Users should only have access to data and projects that pertain to them. Never share additional rights with a user. For instance, a moderator shouldn’t get access to admin-level data. This will help companies keep their data secure and limit unapproved changes. Furthermore, it allows project instructions and content to be risk-free. Before assigning a role, admins should make sure what tasks that user will perform on Redmine. When they have limited capabilities, they can’t take actions that go beyond what their roles call for.
2. Limit Numbers of Admins
Many experts suggest that companies should have one administrator with complete access. An admin should be a trusted member of the company. Therefore, companies should choose admins carefully. It is possible to have more than one admin in Redmine. But, assigning more than three admins doesn’t seem practical.
Some companies set roles that allow more access than what is given to an admin. Call it ‘super admin’ as it allows advanced control over the tool. Admins and super admins should use strong usernames and passwords to secure their access. Keep in mind, users with admin roles have the ability to add and remove users on Redmine. So business managers should analyze the risks and maintain proper regulation.
3. Review User Roles and Capabilities
Managers or admins should review user roles on a timely basis. Redmine offers a list of roles and permissions that makes it easier for admins to check users’ capabilities. Furthermore, admins should evaluate the assigned roles on a daily, weekly, or monthly basis. If they find a user that doesn’t belong to a role they are in, managers should immediately remove them.
Conclusion
Redmine offers a strong interface, especially when it comes to managing roles and permissions. Because Redmine offers maximum security, many business owners trust this tool. If you want to systematically organize your data or streamline business functionalities while preventing vulnerabilities, you should go with Redmine.
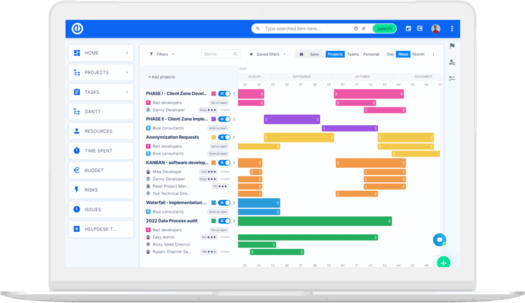
The ultimate Redmine upgrade? Easy.
Get all powerful tools for perfect project planning, management, and control in one software.