The dangers of unsupported servers from Jira Software
Hackers attacked Atlassian Confluence Data Center and Server primarily in two significant waves related to critical vulnerabilities disclosed in 2023 and exploited actively by early 2024. Do you know what happens with unsupported servers and your company’s data? The backbone of many businesses relies heavily on robust software solutions like Jira. However, the foundation upon which these systems operate—the servers—often goes overlooked.

Table of contents
Server support matters: A wake-up call for Jira and Confluence users
No more Jira on-premises: End of life Data Center after 2029
Overview of unsupported servers
The risks of staying on unsupported Servers with Jira Software
1. Security breaches and cyber threats
2. Compatibility issues
3. Lack of updates and support
4. Compliance and legal concerns
5. Best practices for mitigating risks
Protect your project data: Use Jira on-prem alternative
TL;DR
The recent Jira Cloud outage and rising security threats to Atlassian's Server products highlight the risks of vendor lock-in and unsupported infrastructure — making now the time to consider secure, on-premises alternatives like Easy Redmine.
Server support matters: A wake-up call for Jira and Confluence users
In 2023, Atlassian Confluence Data Center and Server were under hackers' attack rated 10.0 on the CVSS severity rating system. This allowed remote attackers to create unauthorized Confluence administrator accounts and access Confluence servers. Thousands of users were left with no access to products for weeks.
Since Atlassian announced the end of server support on 15 February 2024, it has brought some challenges for companies to manage their server data issues. This article sheds light on the critical importance of utilizing supported servers, particularly concerning software like Jira and the inherent risks associated with neglecting this aspect of infrastructure management.
Not to mention that recent major outage of AWS, affecting Jira Cloud and Confluence on 21 October, 2025 locked out thousands of teams who had followed Atlassian’s push toward the Cloud, highlighting the risks of relinquishing control and relying solely on a single provider.
No more Jira on-premises: End of life Data Center after 2029
On September 8, 2025, Atlassian announced that it was sunsetting its Data Center products, including Jira Data Center, Confluence Data Center, and several others, as part of its strategic shift to focus on Atlassian Cloud.
The phase-out process is planned as a phased three-year transition till 2029, as described in an article about Jira alternatives on-premises.
Overview of unsupported servers
Unsupported servers refer to those operating on outdated or unsupported software versions, typically lacking necessary updates, patches, and vendor support. Despite the clear warnings and risks, organizations sometimes opt to remain on unmaintained servers due to various reasons, including budget constraints, perceived stability, or a lack of understanding of the potential consequences.
The risks of staying on unsupported Servers with Jira Software
1. Security breaches and cyber threats
The servers that are not supported are akin to opening doors for cyber attackers, inviting breaches, and data theft. A recent critical vulnerability in the Jira Service Management Server and Data Center serves is a stark reminder of the dangers posed by unsupported systems. Hackers, including state-sponsored groups, actively exploited such weak points to infiltrate networks and compromise sensitive information.
Microsoft mentioned that Chinese state-backed hackers exploited a “critical”-rated zero-day vulnerability in Atlassian software to break into customer systems. What happened with Atlassian in 2023 in a nutshell?
It was noticed the security flaw was being exploited starting from September 14, 2023, which was before Atlassian announced it publicly on October 4, 2023. These cyber-threats allowed malicious actors to remotely execute arbitrary code (RCE), bypass security measures, and gain unauthorized access to sensitive systems and data.
Therefore there is the risk of remote code execution, where attackers could manipulate data, compromise system integrity, and pose a significant threat to organizational security. Exploiting these weaknesses also exposes organizations to data breaches, enabling attackers to exfiltrate sensitive information like customer data and intellectual property, leading to reputational damage and financial losses.
Furthermore, these weaknesses could facilitate credential theft, allowing attackers to harvest user credentials and escalate their privileges within the network, expanding the scope of their malicious activities. The compromise of software in general opens the door to supply chain attacks, where adversaries exploit trusted relationships and software dependencies to infiltrate target networks.
Lastly, the mentioned data exposure risks can lead to persistent cyber threats by enabling attackers to establish long-term access within the network, evade detection, escalate privileges, and exfiltrate data over an extended period, prolonging the recovery process and exacerbating the impact of their attacks.

2. Compatibility issues
Operating on unmaintained servers can trigger compatibility issues, especially regarding other software and plugin integrations. This can disrupt workflows, hinder collaboration, and ultimately impede productivity. The repercussions extend beyond inconvenience, potentially causing financial losses and reputational damage.
Let´s take a look at the most probable issues:
- Integration disruptions: Unsupported servers can lead to compatibility issues with other software and plugins, disrupting seamless integrations and workflows. In the case of the Jira Service Management Server and Data Center, outdated server versions may not be compatible with the latest plugin updates or third-party integrations, hindering collaboration and productivity.
- Workflow interruptions: Compatibility issues stemming from unmaintained servers can interrupt critical workflows and business processes, causing delays, errors, and inefficiencies. For organizations reliant on Jira for project management and issue tracking, any disruption in system functionality can have cascading effects, impacting project timelines, customer satisfaction, and overall operational efficiency.
- Plugin incompatibility: The use of unendorsed servers may render existing plugins incompatible or unstable, limiting the functionality and effectiveness of the Jira platform. This can impede the adoption of new features, hinder customization efforts, and frustrate users accustomed to specific plugin functionalities, ultimately diminishing the value proposition of the software.
- API limitations: Unmaintained servers may lack support for newer APIs and functionalities introduced in subsequent software versions, constraining organizations' ability to leverage advanced capabilities and integrate with modern tools and technologies. This limitation stifles innovation, inhibits digital transformation initiatives, and puts organizations at a competitive disadvantage in today's fast-paced business environment.
- Legacy system dependencies: Organizations operating on unsupported servers may find themselves tethered to legacy systems and technologies, making it challenging to modernize and adapt to evolving business requirements. This dependency hampers agility, inhibits scalability, and increases technical debt, as organizations struggle to maintain outdated infrastructure and navigate complex integration landscapes.

Easy Redmine is fully GDPR‑compliant, certified to ISO/IEC 27001:2022 and ISO/IEC 27017 standards, and is NIS2‑ready
“Atlassian seems to be unable to grant even partial access to the data customers have or give any snapshots. I talked with customers who explicitly requested snapshots of key documents they urgently needed: Atlassian could not provide even this before they would get around to a full restoration. A reminder to never store anything mission-critical not just in Confluence or Jira, but in any SaaS without a backup independent from the SaaS vendor”, wrote Gergely Orosz in his article.
3. Lack of updates and support
Regular updates and support from software vendors are crucial for maintaining system integrity and security. Unsupported servers deprive organizations of these essential lifelines, leaving them vulnerable to emerging threats and lacking access to critical patches and fixes.
Consequently, businesses risk falling behind, unable to leverage new features or address evolving security challenges effectively.
- Security patching deficiency: Unmaintained servers deprive organizations of essential security patches and updates provided by software vendors. Without timely patches to address known vulnerabilities, organizations remain exposed to exploitation by malicious actors seeking to exploit weaknesses in the software. This lack of security updates leaves systems susceptible to data breaches, unauthorized access, and other cyber threats, posing significant risks to organizational security and data integrity.
- Performance degradation: The absence of updates and support for unsupported servers can result in performance degradation over time. Without access to bug fixes, performance enhancements, and optimizations provided through regular updates, organizations may experience system slowdowns, instability, and compatibility issues, undermining user experience and productivity. This degradation can impact critical business operations, disrupt workflows, and erode customer satisfaction, ultimately impeding organizational growth and competitiveness.
- Functional limitations: The mentioned issue about the server may lack access to new features, functionalities, and enhancements introduced in subsequent software versions. This limitation restricts organizations' ability to leverage the full capabilities of the software, hindering innovation, process improvements, and competitive differentiation. Moreover, the absence of support for newer technologies and standards may impede integration efforts, thwart interoperability with third-party systems, and constrain organizations' ability to adapt to changing business requirements and market dynamics.
- Vendor abandonment risk: There is a huge increase in the risk of vendor abandonment, wherein software vendors cease providing updates, support, and maintenance for older software versions. In such cases, organizations are left without recourse, forced to rely on outdated and vulnerable software without any avenue for remediation or recourse. This scenario exposes organizations to significant liabilities, as they may be held accountable for security breaches, compliance violations, and service disruptions resulting from continued use of unsupported software.
4. Compliance and legal concerns
Staying on servers that are not supported properly can land organizations in hot water with regulatory bodies and industry standards.
Failure to comply with regulations such as GDPR or industry-specific mandates can result in hefty fines, legal disputes, and tarnished reputations. Ignoring these compliance requirements is akin to playing with fire, inviting severe repercussions that can cripple even the most resilient enterprises.
5. Best practices for mitigating risks
To fortify cyber security and enhance system resilience, it's crucial to embrace a comprehensive strategy encompassing regular software assessments, infrastructure modernization, stringent security protocols, and ongoing personnel training:
- Regularly assess and update software: We strongly recommend conducting regular assessments of software infrastructure to identify security gaps and prioritize updates. Establish a proactive patch management process to ensure timely deployment of security patches and software updates, reducing exposure to known risks and vulnerabilities.
- Invest in modern infrastructure: This step will help you benefit from ongoing vendor support, security updates, and performance enhancements. Migrating to supported servers and platforms provides organizations with access to the latest features, functionalities, and security measures, enhancing resilience against evolving threats.
- Implement robust security measures: Apply strong security protocols including firewalls, intrusion detection systems, and endpoint protection solutions, to defend against cyber threats and mitigate the impact of security breaches. Adopt a multi-layered security approach to safeguard critical assets and data from unauthorized access, exploitation, and compromise.
- Educate and train personnel: Make your colleagues and all relevant people in line with understanding of the importance of software updates, security best practices, and risk mitigation strategies. Foster a culture of security awareness and accountability across the organization, empowering employees to recognize and report potential security threats and incidents.

Protect your project data: Use Jira on-prem alternative
The Jira Server data loss incident has underscored the critical importance of robust data management practices and disaster preparedness in today's digital landscape. As organizations reassess their reliance on cloud-based solutions and prioritize data security and system reliability, there's a growing demand for on-premises alternatives that offer both flexibility and peace of mind.
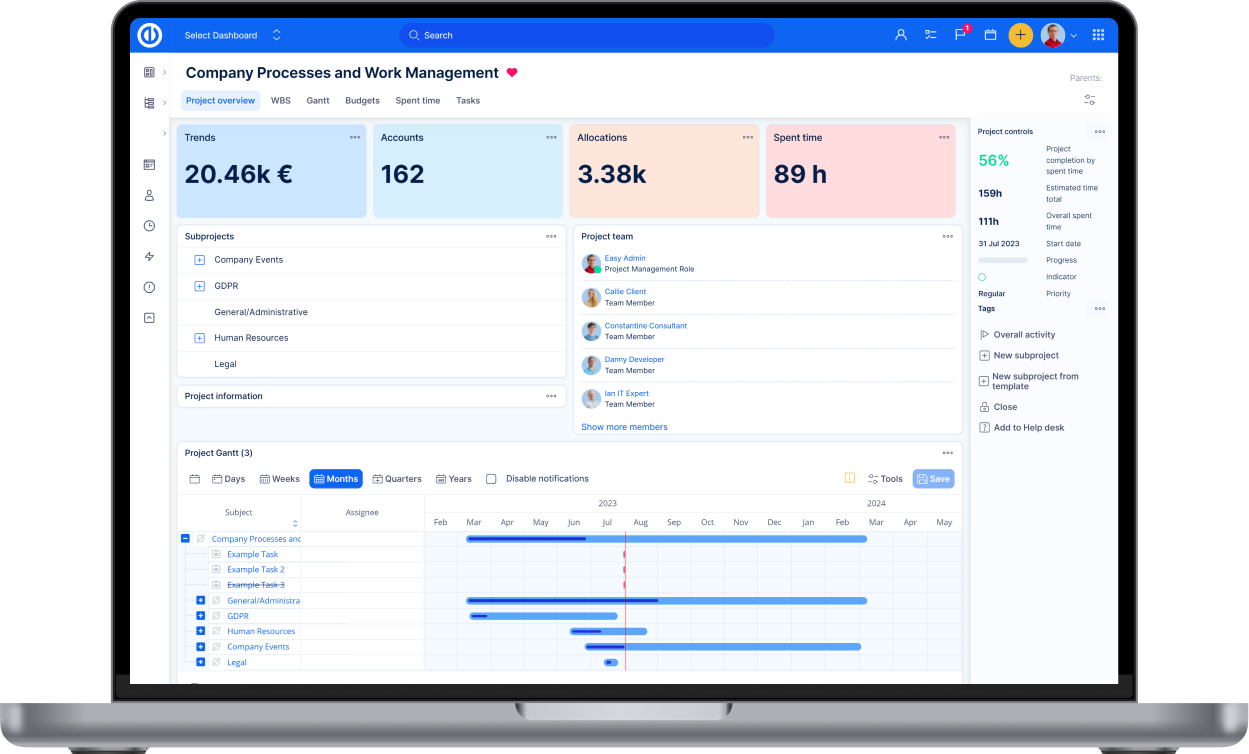
In light of these considerations, we invite you to explore Easy Redmine—an alternative to Jira on-prem, secure alternative to cloud-based project management solutions. With its full-stack capabilities and comprehensive project management features, Easy Redmine empowers organizations to take control of their project data, streamline collaboration, and enhance productivity while maintaining data sovereignty and security.
Jira Cloud was down — and the irony is hard to miss. Atlassian spent years pushing customers to the Cloud, calling it the future. If Cloud is truly the future, the outage incident raises urgent questions about preparedness, independence and whether organizations should explore on-premises or hybrid alternatives.
Take the proactive step towards securing your project management workflows and safeguarding your valuable data by trying Easy Redmine demo or contacting our team for consultation.